In today’s risk-conscious environment, retiring IT assets isn’t just about removing old hardware, it’s about protecting sensitive data, ensuring regulatory compliance, and maintaining operational integrity. At the heart of every modern IT Asset Disposition (ITAD) program is a documented chain of custody: a secure, traceable process that tracks every asset from pickup to final disposition.
What is a Documented Chain of Custody?
A documented chain of custody is a formal record that details:
- Where each asset is at every stage
- Who has handled it
- What actions were taken (e.g., data wiping, resale, redeployment, components recovery, shredding, recycling)
This documentation is essential for proving due diligence, especially in industries governed by strict data protection laws like GDPR, CCPA, and emerging AI governance frameworks. A well-documented process ensures audit readiness and provides peace of mind that assets are being managed responsibly.
How ITAD Companies Ensure Chain of Custody
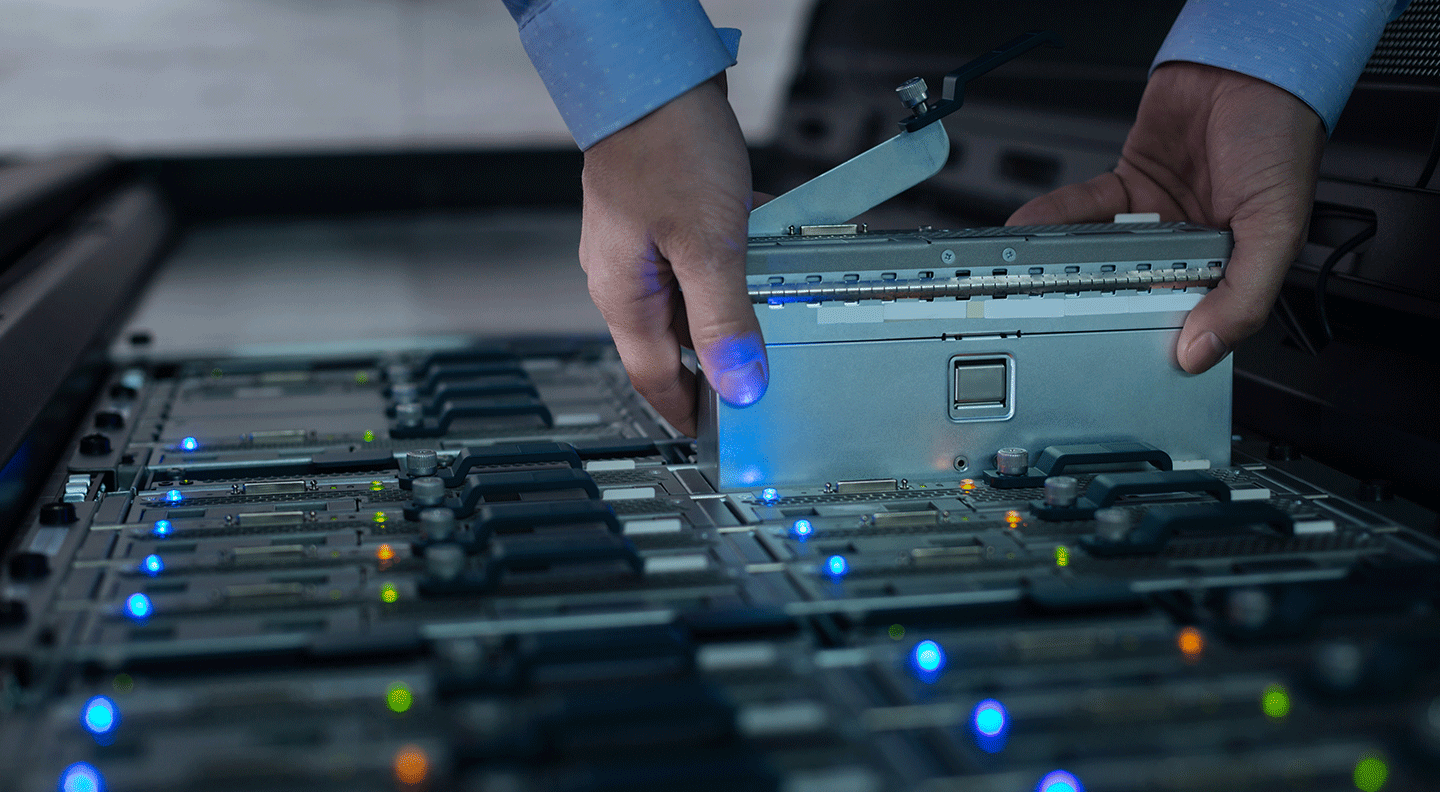
Leading ITAD providers implement the following to maintain a secure and documented chain of custody:
- Serialized Asset Tracking: Each device is tagged and tracked throughout its lifecycle.
- Secure Transportation: GPS-tracked vehicles and vetted personnel ensure safe transit.
- Controlled Processing Facilities: Access-controlled environments prevent unauthorized handling.
- Certified Data Destruction: Adherence to standards like NIST SP 800-88 ensures proper sanitization.
- Real-Time Reporting: Clients receive detailed reports and certificates of destruction.
Compliance and Certifications that Support Documentation
Top-tier ITAD companies align with globally recognized standards to reinforce their documented processes:
- Data Security: NIST SP 800-88
- Environmental Responsibility: R2v3, e-Stewards, ISO 14001
- Quality and Safety: ISO 9001, ISO 45001
- Security: ISO 27001
These certifications validate that the chain of custody is not only secure but also compliant with industry best practices.
The Advantage of a Single-Source ITAD Provider
Using one provider for all ITAD services, including collection, transport, data destruction, refurbishment, and recycling, ensures:
- Consistent documentation across all stages
- Fewer handoffs and reduced risk of asset diversion
- Centralized oversight and accountability
This unified approach strengthens the chain of custody and simplifies compliance management.
SLS: A Model for Documented Chain of Custody
Sims Lifecycle Services (SLS) exemplifies best practices in chain of custody management. With global reach, certified Circular Centers, and advanced digital tracking, SLS ensures that every asset remains within a secure, documented network. Clients benefit from:
- Full visibility into asset handling
- Certified data destruction
- Transparent, audit-ready reporting, including Certificates of Destruction and Certificates of Data Destruction.
By partnering with SLS, organizations gain a trusted ITAD partner committed to data protection, value recovery, and sustainable outcomes.
Gain end‑to‑end control with ITAD+™
Track every asset. Verify every wipe. With certified chain of custody and indemnification, you stay audit-ready at all times.
More Articles
-

Maximize Value from Retired Tech
Read more: Maximize Value from Retired Tech -

Why the Secondhand Laptop Market Is Surging in 2026
Read more: Why the Secondhand Laptop Market Is Surging in 2026 -
Global Data Center Decommissioning
Read more: Global Data Center Decommissioning
