ITAD FAQs
Frequently asked questions
What are the best practices for data destruction?
Industry-Recommended Data Destruction Methods
NIST 800-88 is the most commonly recognized industry standard for compliant data destruction. Initially released as NIST 800-88 r1 in 2014, in 2025 an updated version, NIST 800-88 r2 is now available.
Here are the most recognized and widely used data destruction methods, each with different implications for security, reuse potential, and environmental impact:
Erasure
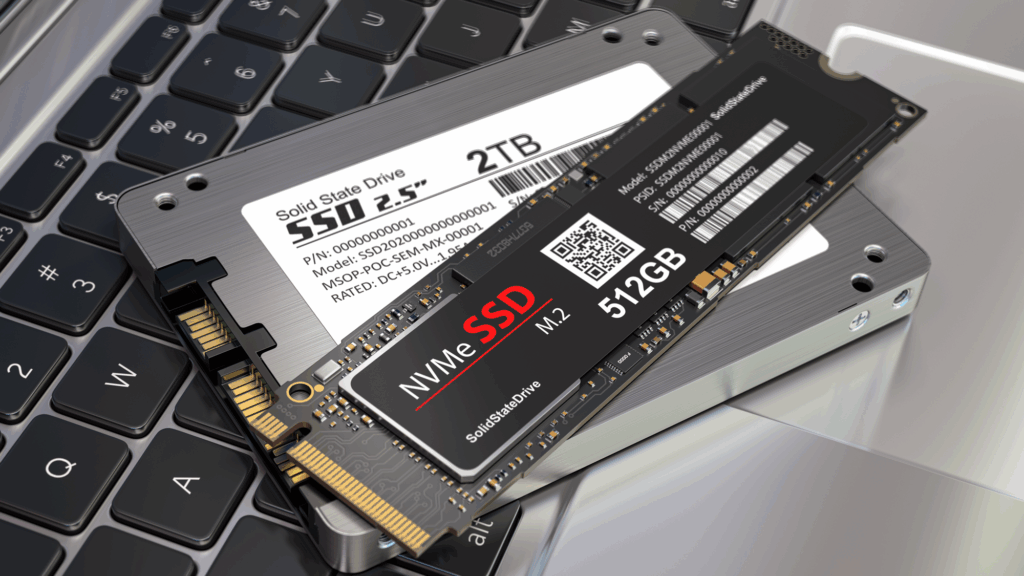
Software-Based Data Erasure (Wiping)

USE CASE: Balances data security with financial and sustainability objectives.
How it Works
Commercial tools like Blancco overwrite all data on a device following industry-standard protocols.
Benefits
- Allows drives to be reused, maximizing asset value recovery
- Supports circular economy by avoiding the carbon footprint of new device production
Best Practice
Data erasure should be verified, typically through software validation.
Shredding
How It Works
Devices are physically destroyed by shredding, crushing, drilling, or punching.
Benefits
- Shredding is a quick way to destroy storage media. Physical destruction of the drive renders data recovery near impossible. The size of the shredded material dictates whether the method is compliant to NIST 800-88 standards.
Drawback
Prevents any possibility of reuse or resale.
Physical Destruction (Shredding)

USE CASE: Ideal for end-of-life drives or equipment not suitable for reuse.
Degaussing
Degaussing

USE CASE: Commonly used on-site in classified, financial or health data environments.
How It Works
Applies a powerful electromagnetic field to erase the data by disrupting the magnetic domains on a hard drive or tape.
IMPORTANT NOTE: Degaussing is only effective on magnetic hard disk drives (HDDs) and tapes. It is not effective for wiping solid state drives (SSDs).
Benefits
- Fast and effective for high-risk or regulated data stored on magnetic drives.
- Frequently paired with shredding for visual confirmation of data destruction.
Best Practice
Renders drives unusable; they cannot be resold or reused
Certification: A Compliance Must-Have
No matter which method you use, proper documentation is critical to proving compliance with data privacy regulations like GDPR, HIPAA, CCPA, or SOX.
Always request a Certificate of Data Destruction (CODD) that includes:
- Unique asset identifiers (e.g., serial numbers)
- Destruction method used
- Date and location of destruction
- Verification that data was destroyed compliant with NIST 800-88 or another accepted standard
These records are essential during compliance audits and demonstrate that your organization took proper steps to dispose of sensitive data responsibly and securely.
An effective data destruction program protects your organization from data breaches, legal risk, reputational damage, and non-compliance penalties.
By aligning your practices with industry best standards and working with certified ITAD providers, you not only protect sensitive data – you also gain peace of mind.
Data Destruction Services
SLS guarantees complete digital data destruction services and provides Certificates of Data Destruction as required.
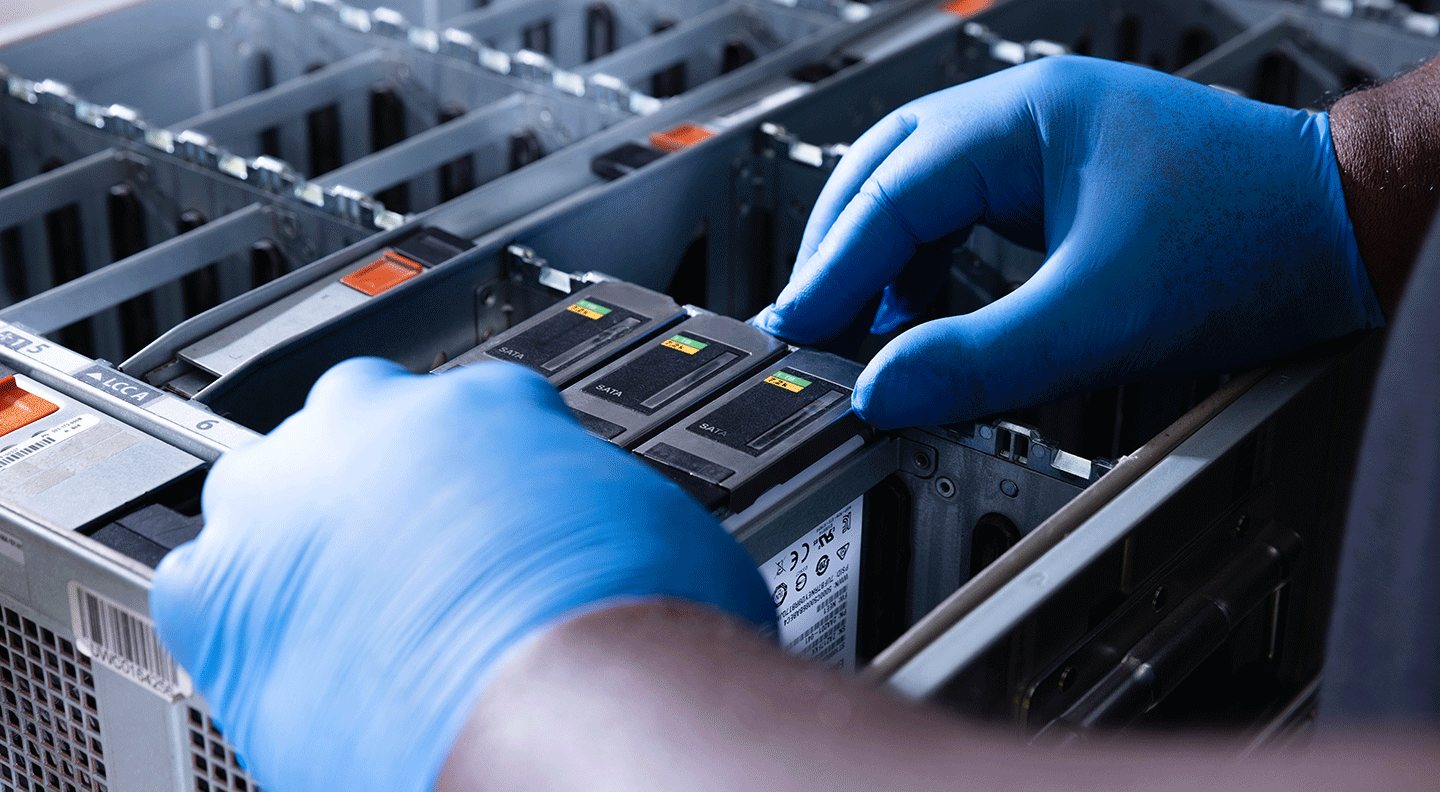
On-Site Data Destruction
Need us to come to you? Let’s schedule your secure, on-site shredding project today.
Bulk Services at SLS
Our Circular Centers handle bulk erasure or shredding with full chain-of-custody and certified results.